Feel at ease knowing your devices are always secure
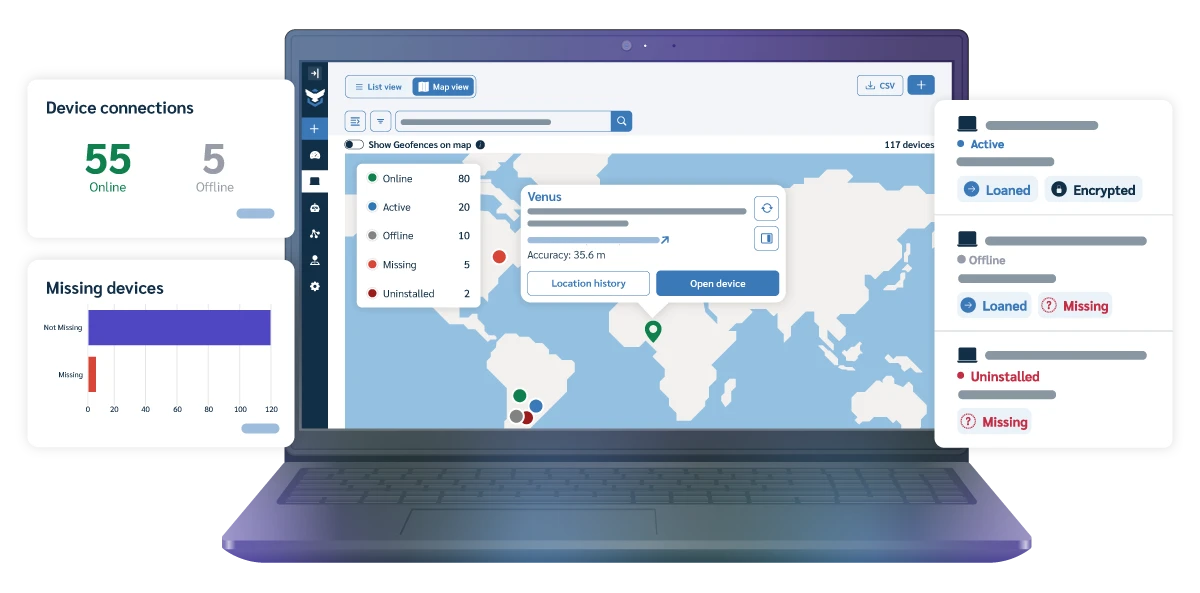
It’s simple: devices go missing, data is vulnerable, and we have the tools to help you handle it. Save time and worry less with a 24-7 device tracking & security solution made for IT Admins.
What is Prey?
A single-platform Security Service that aims to solve the Tracking and Management needs of organizations of all sizes (and different backgrounds!)
Also, Prey is a dedicated group of people happy to give personalized assistance!
Prey
Full Suite
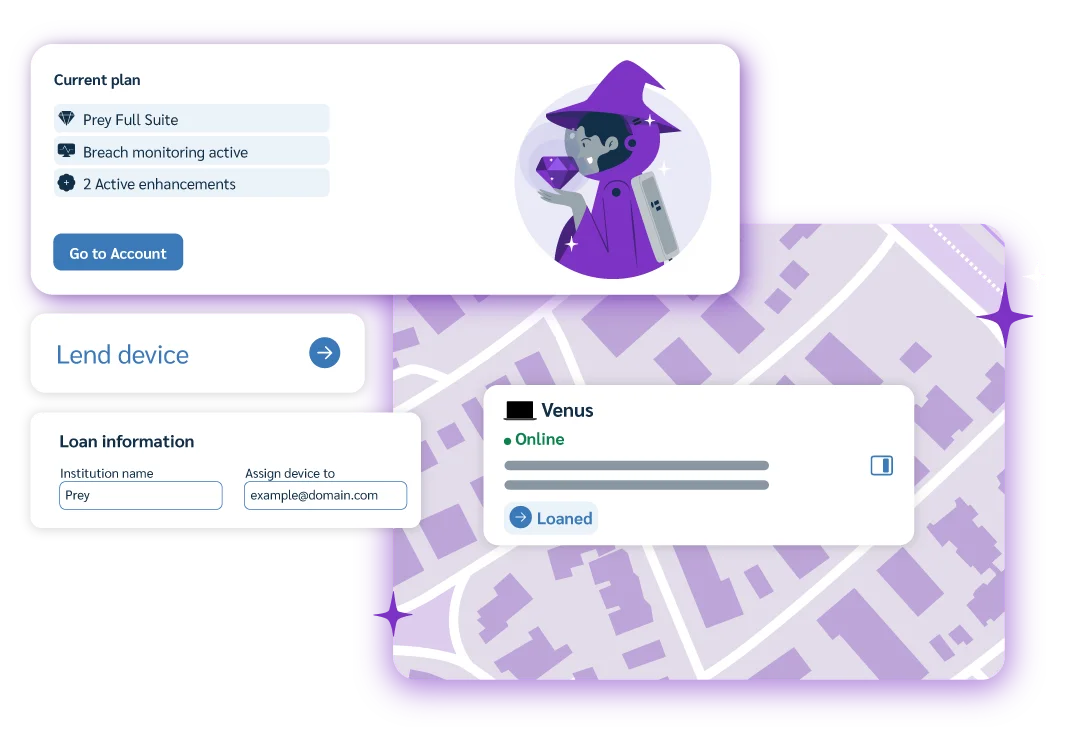
Tracking, Security and Management all in one.
Prey
Protection
Active Tracking with a layer of data and device Security.

Prey
Tracking
Active Tracking and Location for device fleets.
Who Benefits from Prey
Designed to support different teams and goals, Prey is a multi-OS, smart security tool with affordable solutions for companies at every scale.
Busy Device Admins
Overwhelmed with device management tasks? Get streamlined support with a single platform to assign, loan and label devices.
Compliance Seekers
Handling sensitive data from finance, health, and government sectors? Get data protection tools to boost security in high-stakes industries.
Remote Teams
Managing devices in several remote locations? Our device monitoring tools keep networks secure and responsive.
Large Fleet Managers
Managing diverse devices across teams? Simplify with our all-in-one monitoring and management solution, tailored for varied needs.
MSP Multitaskers
Juggling customer safety and organization? Our multi-tenant tool streamlines client management, keeping data separate and secure.
And Everyday People!
We know your gadgets are essential to stay connected, study, work and even play! Secure your devices and data, in a single app.
Our users said it best!
Take a look at some of our most loved capabilities as recognized by G2 and our users.
Ease of Use
A service that offers intuitive design, streamlined navigation and customizable features enabling users to accomplish tasks effortlessly.
Quality of Support
A prompt and knowledgeable assistance. Proactive outreach empowers users, making sure their needs are met efficiently and effectively.
Ease of Setup
With an intuitive onboarding and comprehensive guidance, the initial configuration is a streamlined process with minimal effort.
























