Locate every device. Beat every breach. Ace every audit.
Always-on tracking, remote wipe and breach monitoring built for IT teams who need to act fast and stay compliant.


























Managing devices shouldn't keep you up at night
IT teams face challenges that grow alongside their fleet. Sound familiar?
Lack of fleet visibility
How many devices do you actually manage? Where are they right now? Without a centralized system, blind spots multiply and become a latent risk.
Data exposure risk
A missing laptop can mean thousands of exposed records. Without the ability to act remotely, your vulnerability window grows by the minute.
Growing legal pressure
New data protection regulations demand proof of control over your devices. Without evidence of management, fines and legal liability land on your team.
Everything your fleet needs,
without unnecessary bulk
Four core strengths. One platform. Built for the way IT actually works.
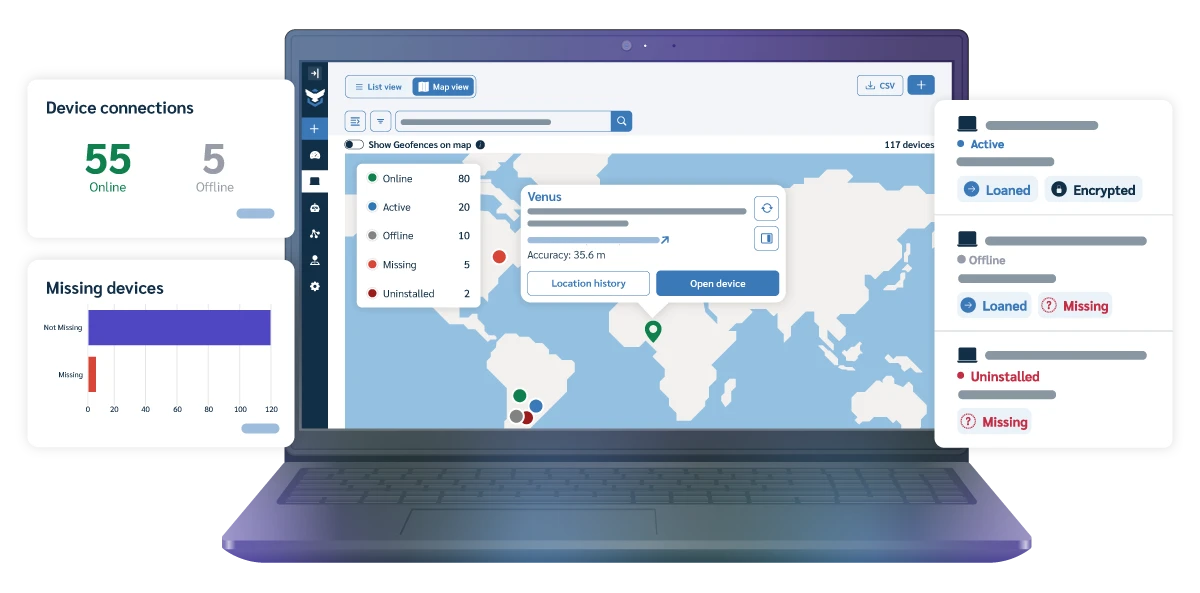
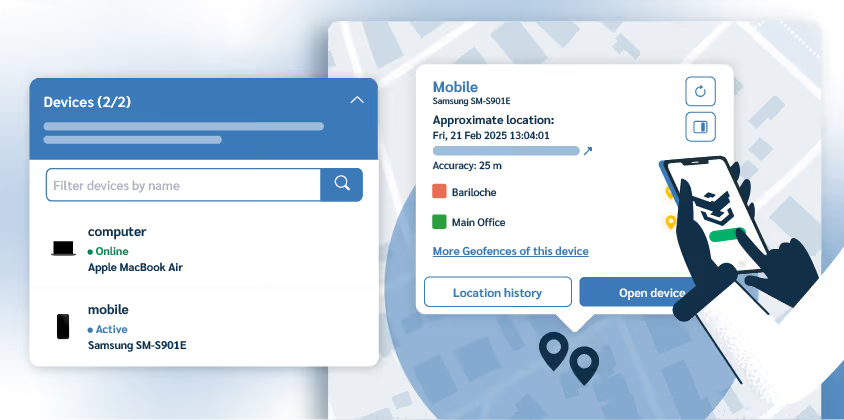
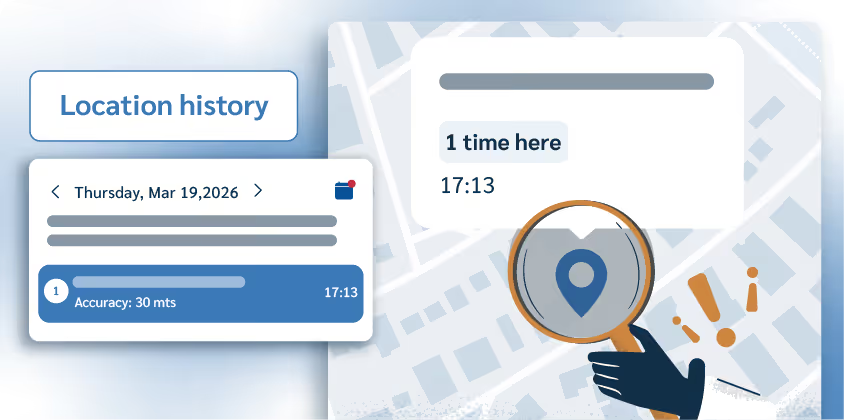
Always-on, full fleet visibility
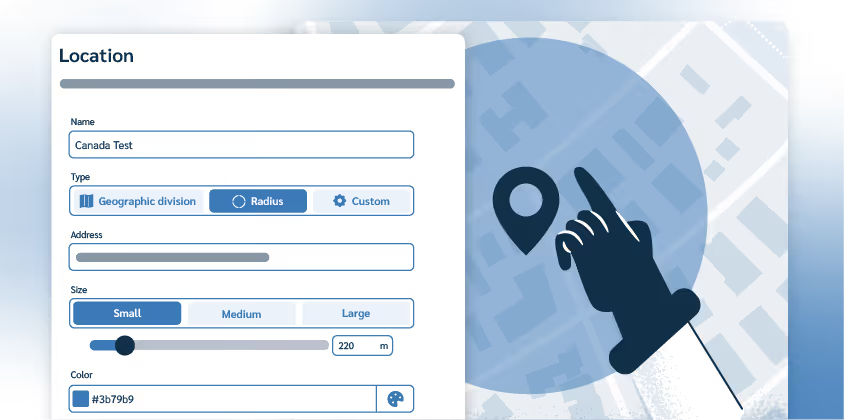
Ongoing GPS and Wi-Fi triangulation across Windows, macOS, Linux, Android, iOS, and Chromebook. Set geofences, get instant alerts, and reconstruct movement when devices go off-script.
Active GPS + Wi-Fi tracking. No more on demand and delayed pings.
Location history. Logs device movements going back up to a year.*
Geofences. Safe perimeters with custom automatic actions and alerts.
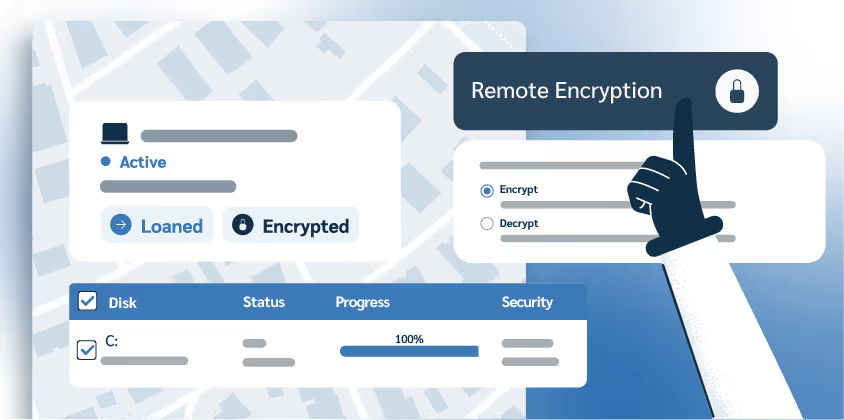
From exposure to containment in just a few clicks
A robust security toolbox with ready-to-deploy immediate actions. Freeze, restore and encrypt devices, enforcing security measures fleet. Every action logged, every step audit-ready.
Remote lock. Freeze any device instantly.
Custom wipe. Delete specific files, folders, or the entire disk.
Windows BitLocker. Automated encryption plus key management.

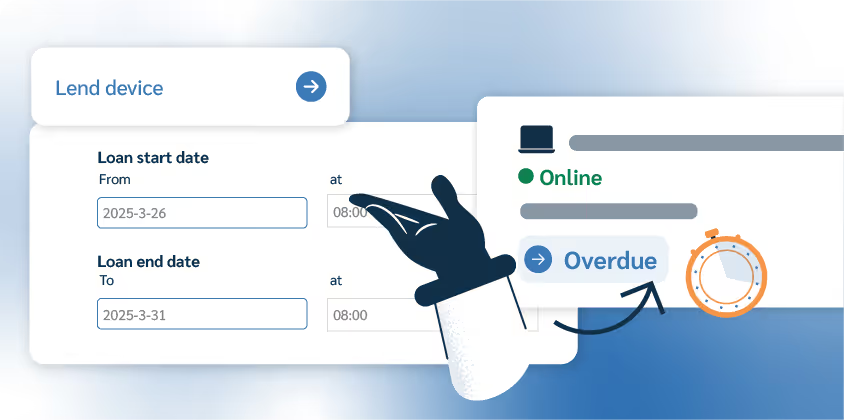
Upgrade spreadsheet inventories
Automatically register hardware and software. Assign devices to admins, tag by location or department, loan devices to users, and generate exportable audit reports.
HW inventory. Every device, every data point, across every OS.
Loan manager. Assignment, due dates, automatic lockouts on overdue.
Custom fields & groups. Appoint devices by admin, department, role, etc.

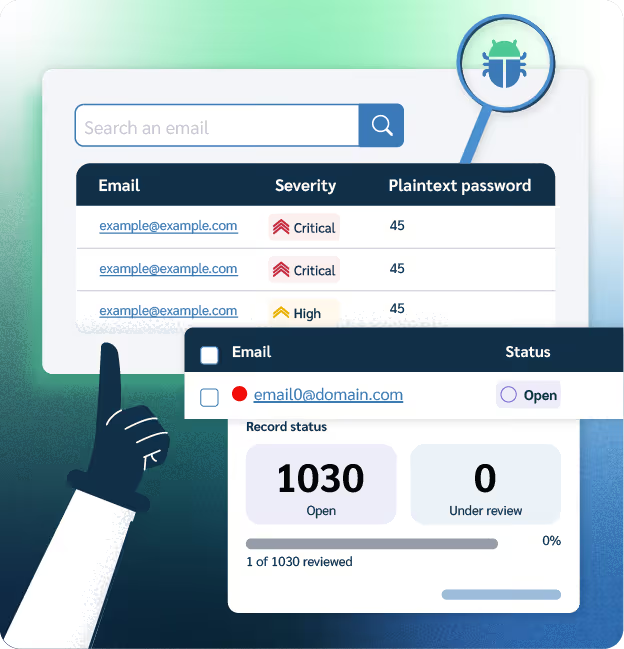
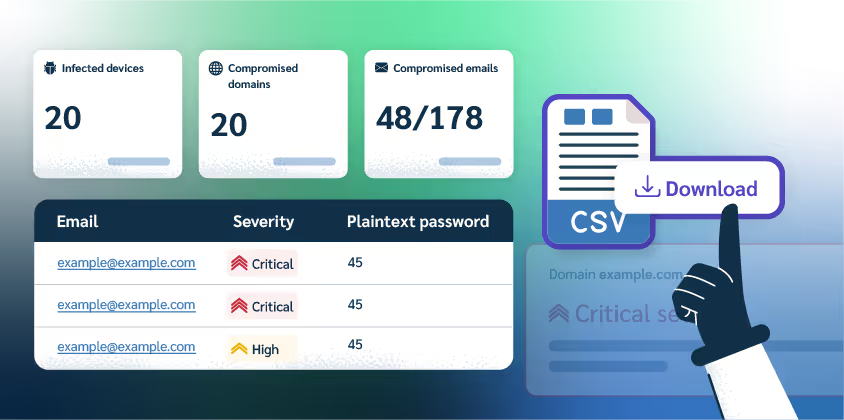
Learn about data leaks first
Continuous dark web monitoring for your business. Get weekly reports detailing severity scores, exposed data, and the exact accounts to reset before attackers can exploit them.
Domain-wide secanning. Continuous monitoring for every company email.
Severity-scored alerts. Automatic risk ranking that saves triage time.
Pre-prioritized insights. No analysis required, focus instantly on top threats.
Built for when devices won't behave
From distributed teams to dark web breaches: six scenarios where Prey shows up, so your team doesn't have to scramble.
Built for teams with real stakes in every device
Whatever your role looks like on a bad day, Prey adapts to your workflow.
IT Admins
Drowning in onboarding, offboarding, and missing devices?Assign, loan, label, and lock from one panel. Stop chasing devices across spreadsheets.
Security Teams
Endpoints scattered across home networks and coffee shops?
Real-time location, instant remote wipe, and dark web breach alerts give your SOC the visibility it's missing.
Compliance & Risk
Auditor knocking on a Friday? Pull device action logs, encryption status, and incident reports in minutes, there's no need to plan for it weeks ahead.

How Rock Valley College hit a 95% laptop recovery rate.
Rock Valley College runs a 1:1 device program with hundreds of students. With Prey's loan parameters and automatic lockouts, they recovered 95% of their fleet in a single semester.
Trusted by IT teams in 170+ countries.
Since 2009, Prey has helped IT and security teams protect, track, and manage every device in their fleet, without the enterprise price tag.





Based on Prey customer data, Q1 2026. See verified reviews on G2 →
“The product has helped us meet our geolocation needs, control the equipment, and improve security in its management."
Already have an MDM?
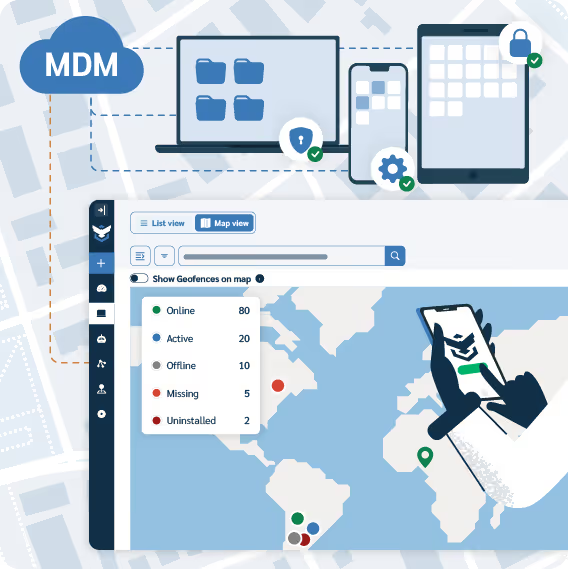
Prey is the tracking layer you're missing
Intune, Jamf, NinjaOne are policy engines. They can't tell you where every device is right now, hand auditors proof of a wipe, or watch the dark web for leaked credentials. Prey fills those gaps without replacing your stack.
Active tracking. Nonstop device visibility with auto-saving logs and map views
Beyond the device. Weekly dark web monitoring reports that standard MDMs don't provide.
Intruder-resistant encryption. BitLocker makes stolen Windows devices completely unreadable.
Audit-ready evidence. Verified location stamps and the logs you need to validate compliance.
Built for teams navigating:
HIPAA | FERPA | GDPR | ISO 27001 | PCI
"I love Prey's ease of use, lightweight nature, and superior mapping capabilities compared to Intune."
Alan
"We like (Prey) because it's outside of our MDM platforms. So if they do become disconnected from Intune or Jamf, Prey still works."
Javas
