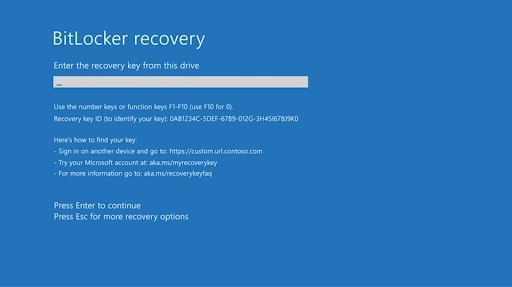
It usually happens on a Tuesday. Someone reboots after a Windows update, or IT pushes a BIOS patch overnight, and the next morning the laptop boots to a blue screen demanding a 48-digit BitLocker recovery key. No desktop, no login box, just a field, a Key ID, and a blinking cursor.
The first instinct is panic, then suspicion: is this malware? It isn't. BitLocker encryption is doing its job. Something about the device changed enough that it no longer trusts the boot environment, so it sealed the drive and asked for proof you're allowed in. The data is fine. It's just locked behind a number you may already have without knowing it.
For an individual, this is a bad morning. For an IT team, it's a recurring ticket with real stakes: an encrypted drive with no recoverable key is, for practical purposes, a wiped drive. This guide covers all seven places your BitLocker recovery key might be stored, how to match the Key ID on screen to the right key, why the prompt appeared in the first place, and the honest answer to the question people Google at 9 a.m.: can I just crack it?
What Is a BitLocker Recovery Key?
BitLocker is a full-volume encryption feature built into Windows. It protects data by encrypting the entire drive, so even if someone gains physical access to the device, they cannot read the files without the correct credentials.
According to Microsoft, the BitLocker recovery key is a unique 48-digit numerical password generated when BitLocker is first enabled on a device. It unlocks the encrypted drive when BitLocker cannot automatically verify that access is authorized -- for example, after hardware changes, failed PIN attempts, firmware updates, or a suspected security event.
The key is created once. Where it gets stored depends entirely on how BitLocker was set up and whether the device is personally owned or managed by an organization.
The Key ID is not the key. The recovery screen shows two things: a short Key ID (a string like A1B2C3D4) and a field for the 48-digit key. People type the Key ID into the field and get rejected. The Key ID is only a label -- its job is to tell you which key matches this specific drive, which matters when a device or account has several keys stored against it. Use the Key ID to look up the right key, then enter the 48 digits.
Quick win: before doing anything else, photograph or write down the Key ID from the recovery screen. Every method below uses it to confirm you are entering the right key, and on a multi-key device it is the difference between unlocking the drive and locking yourself out further.
Where Is My BitLocker Recovery Key? 7 Locations
Work through these methods in order. Personal users will most likely find their key in Method 1 or 5. IT admins managing company devices should check Methods 2, 3, or 4 first.
1. Microsoft Account (Personal and Home Devices)
If BitLocker was enabled while you were signed into a Microsoft account -- the default on most Windows 10 and 11 home devices -- the recovery key was automatically uploaded online.
Steps:
- Open a browser on any device and go to aka.ms/myrecoverykey.
- Sign in with the Microsoft account linked to the encrypted device.
- Your BitLocker recovery keys will be listed with the device name and a key ID.
- Match the key ID shown on your recovery screen to the correct entry in the list.
- Copy the 48-digit recovery key and enter it on the locked device.
Note: This only works if you were signed into a Microsoft account when BitLocker was first activated. Devices set up with a local account will not have a key stored here.
2. Azure AD / Microsoft Entra ID (Work or School Devices)
If your device is joined to Azure Active Directory (now Microsoft Entra ID) -- common for company-issued or school-issued laptops -- the recovery key is stored in your organization's Azure AD tenant.
For end users:
- Go to myaccount.microsoft.com/device-list from any browser.
- Sign in with your work or school Microsoft account.
- Select your device from the list.
- Click View BitLocker Keys.
- Copy the key that matches the key ID on your recovery screen.
For IT admins:
- Sign in to the Microsoft Entra admin center at entra.microsoft.com.
- Go to Devices > All devices.
- Search for the affected device by name or user.
- Select the device and click BitLocker Keys in the left panel.
- Click to reveal the recovery key (keys are partially masked by default).
Admins can also retrieve keys via Microsoft Graph PowerShell: Connect-MgGraph -Scopes BitLockerKey.Read.All then Get-MgInformationProtectionBitlockerRecoveryKey -All.
3. Active Directory (On-Premises Enterprise)
If your organization uses an on-premises Active Directory environment, IT admins can retrieve recovery keys from AD -- provided Group Policy was configured to back them up when BitLocker was enabled.
Steps (IT admins only):
- Open Active Directory Users and Computers.
- Under the View menu, enable Advanced Features.
- Locate the computer object for the affected device.
- Right-click the computer object and select Properties.
- Navigate to the BitLocker Recovery tab to view stored keys.
Admins can also search across all domain devices via PowerShell: Get-ADObject -Filter {objectClass -eq 'msFVE-RecoveryInformation'} -Properties msFVE-RecoveryPassword
Note: Keys are only stored in AD if Group Policy required the backup before BitLocker was enabled on each device.
4. Microsoft Intune (MDM-Managed Devices)
Organizations managing devices through Microsoft Intune can retrieve BitLocker recovery keys directly from the Intune admin center.
Steps (IT admins only):
- Sign in to the Microsoft Intune admin center at intune.microsoft.com.
- Navigate to Devices > All devices.
- Search for the affected device by name or user.
- Select the device and scroll to the Monitor section in the left panel.
- Click Recovery keys to view the BitLocker key.
Intune only stores the key if the BitLocker policy was applied before encryption was enabled. Devices encrypted manually before Intune enrollment may not have their keys there.
5. USB Drive or Printed Copy
During BitLocker setup, Windows offers the option to save the recovery key to a USB drive or print it. If you or your IT team selected one of these options, check these physical locations.
- Search USB drives stored in your desk, IT supply cabinet, or device bag.
- Check printed pages stored with device documentation or in a filing system.
- If found on USB, plug the drive into any Windows device, open the file, and enter the key on the locked device.
This is the only option if the device was set up offline with a local account and no cloud or domain backup was configured.
6. Command Prompt -- manage-bde
If you have access to a working Windows session, you can retrieve the recovery key using the built-in manage-bde command-line tool.
Steps:
- Open Command Prompt as Administrator.
- Run:
manage-bde -protectors -get C:(replace C: with your encrypted drive letter). - Look for the Numerical Password section in the output.
- Copy the 48-digit recovery key listed there.
IT admins can query remote machines using: manage-bde -cn [ComputerName] -protectors -get C:. This requires an active, unlocked Windows session -- it will not work if you are already locked out of the target device.
7. Prey - Centralized Recovery Key Management (IT Teams)
If your organization uses Prey for endpoint management, BitLocker recovery keys are stored and accessible directly from the Prey dashboard -- no need to switch between Intune, Azure AD, and Active Directory consoles.
- When Prey activates BitLocker on a device, it automatically generates and stores the recovery key (encrypted) in your Prey account.
- IT admins can view recovery keys for individual devices from the fleet dashboard at any time.
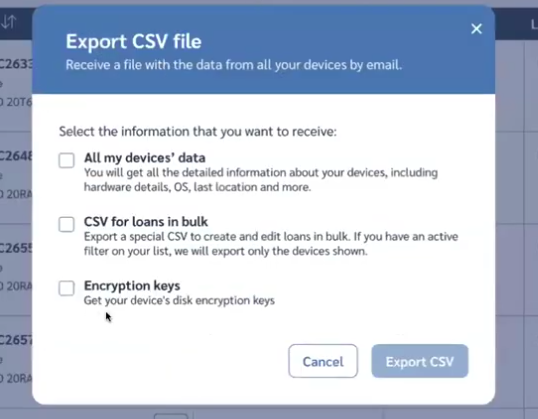
- Keys can be exported as a CSV file for bulk management, helpdesk use, and compliance audits.
- Ideal for organizations that need a single location for recovery keys across a distributed Windows fleet.
These seven methods cover every scenario -- personal Microsoft accounts, cloud-joined work devices, on-premises AD, Intune MDM, physical backups, and direct CLI access. Work through them in order based on how the device was set up.
Why Did BitLocker Suddenly Ask for My Recovery Key?
BitLocker didn't break and you weren't hacked. The recovery prompt fires when something changes the boot environment enough that the TPM (the security chip that normally releases the key automatically at startup) no longer recognizes the device as the trusted machine it sealed the key to. The TPM measures the boot path; when the measurement doesn't match, it refuses to auto-release the key and falls back to recovery.
The usual triggers:
- A BIOS or UEFI firmware update -- very common when IT pushes one fleet-wide overnight.
- Hardware changes: swapping the motherboard, adding or moving a TPM, sometimes even a docking station or a new boot device.
- Boot configuration changes: toggling Secure Boot, changing boot order, or switching between UEFI and legacy.
- A failed or interrupted Windows update that left the boot files in an unexpected state.
- Dual-boot setups where another OS modifies the bootloader.
Understanding the cause matters because it tells you how to stop the cycle. If a BIOS update triggered it, the fix isn't just finding the key once; it's suspending BitLocker protection before the next firmware change so the TPM re-seals cleanly afterward. Running manage-bde -protectors -disable C: suspends protection temporarily, and BitLocker resumes automatically on the next reboot. An MSP that pushes a BIOS update to 60 machines on a Friday night without suspending first spends Monday morning buried in recovery tickets -- all of them avoidable.
Quick win: before any planned BIOS or firmware update, suspend BitLocker protection (manage-bde -protectors -disable C: or the equivalent in your management tool). It re-arms automatically on reboot and saves you a wave of recovery prompts.
What If I Can't Find My BitLocker Recovery Key?
If you have checked all seven locations and still cannot find the key, you have a few last-resort options before accepting that the data may be unrecoverable.
- Try rebooting first. Some BitLocker recovery prompts are false positives triggered by a firmware update or a minor startup anomaly. Rebooting gives Windows another chance to verify the startup environment, and you may be able to log in normally.
- Reverse recent BIOS or hardware changes. If you recently modified BIOS settings, changed boot order, or swapped hardware, reversing those changes may allow BitLocker to resume without the recovery prompt.
- Contact your IT department. For organization-managed devices, IT may have a backup that is not in the locations you checked -- particularly if keys were exported before a system migration or stored in a third-party ITSM tool.
- Check OEM or purchase documentation. Some enterprise device purchases include recovery key documentation. Check the original purchase records or contact the device manufacturer.
- Last resort: Reset the device. If no key is available, you can reset Windows using recovery media. This erases all data on the encrypted drive permanently. There is no technical workaround -- a BitLocker-encrypted drive without the correct recovery key is unrecoverable by design.
This is exactly why storing recovery keys at setup time matters so much. Once they are gone, the data is gone with them.
Can You Crack, Bypass, or Generate a BitLocker Recovery Key?
People search for "crack bitlocker recovery key," "bitlocker recovery key generator," and "unlock bitlocker from cmd without password" for an understandable reason: they're locked out and desperate. The honest answer is the one nobody wants: no, you cannot.
A BitLocker recovery key is a 48-digit number protecting an AES-encrypted volume. Brute-forcing it isn't a matter of finding the right tool; the keyspace is large enough that guessing it is computationally infeasible within any practical timeframe. The "key generators" and "BitLocker finder" tools that show up in search results don't recover your key. At best they read a key that is already accessible on a drive you can already unlock, which doesn't help when you're locked out. At worst they are a security risk.
The command-line route has the same limit. manage-bde and repair-bde are genuinely useful, but they need either the recovery key or the recovery password to do anything. There is no command that bypasses encryption you don't have the credentials for. That is not a flaw; it is the entire point of encryption. If there were a backdoor, the protection would be worthless against the lost-or-stolen-laptop scenario it exists to defend against.
So the real fork is simple. Either the key was escrowed somewhere -- your Microsoft account, Azure AD, Active Directory, Intune, a USB, or a printout -- and you can retrieve it, or it was not, and your only remaining option is to reset the drive, which erases the data. There is no third path.
Quick win: stop searching for crackers and finders; they cannot recover a lost key and some carry malware. Spend that time confirming where your keys are actually escrowed instead.
How to Verify a BitLocker Recovery Key
BitLocker recovery keys should be verified before you need them in an emergency. An invalid key will not unlock your drive when it counts.
Steps to verify in Windows 10 and 11:
- Open the verification tool: Type recovery key into the Windows search box, then select Verify BitLocker Recovery Key.
- Enter your recovery key: Type the 48-digit key and click Verify.
- Wait for verification: This may take a few minutes depending on your system.
- Check the result: The tool will confirm whether the key is valid for the encrypted drive.

How to Store Your BitLocker Recovery Key
The best time to back up your recovery key is right now -- before you need it. Here are the most reliable options:
1. Print it and file it physically
- Print the recovery key and store it in a secure filing cabinet.
- Keep it separate from the device it protects.
2. Save it to a USB flash drive
- Create a file with the recovery key or export it as a PDF.
- Store the USB drive in a safe or secure location separate from the device.
3. Store it on a separate device
- Save the key as a PDF on a second computer or in an encrypted cloud storage service.
- Never store it on the same device it protects.
4. For IT teams: Use Prey for centralized key management
- When Prey activates BitLocker, it automatically generates and stores the recovery key (encrypted) in your Prey account.
- Export all recovery keys as a CSV anytime for compliance, audits, or helpdesk use.
Printing or saving your key to a USB drive is the only option if the device was set up with a local account and no cloud or MDM backup was configured. Do not wait until you need it to find out your backup method failed.
Troubleshooting BitLocker Recovery Issues
The BitLocker recovery screen appears when Windows cannot automatically unlock an encrypted drive. Common causes include hardware changes, firmware updates, BIOS modifications, or failed authentication attempts.
If you are experiencing repeated recovery prompts:
- Check your Microsoft account first: Go to aka.ms/myrecoverykey from another device.
- Verify the key ID: Match the key ID on the recovery screen with the ID in your storage location to ensure you are entering the right key.
- Check your USB drive: If the key was saved to USB, plug it into the locked device and let Windows read it automatically.
- Contact your IT department: For organization-managed devices, IT may have a backup in Azure AD, Active Directory, Intune, or Prey.
- Reset the device as a last resort: If no key is available, Windows recovery options can reset the device -- but all data on the encrypted drive will be permanently lost.
Next Steps
Data security is not just about protecting devices -- it is about protecting the trust your organization places in its technology every day. BitLocker provides a solid first layer of defense, keeping sensitive information safe from unauthorized access. But to get the most out of it, you need smart key management and tools that make encryption effortless at scale.
Prey's Disk Encryption solution works alongside BitLocker, adding centralized control and automation for IT teams managing distributed device fleets:
- Activate and manage: Enable BitLocker across your Windows fleet from the Prey dashboard -- no manual configuration needed on each device.
- Store and retrieve: Recovery keys are automatically captured and stored encrypted in Prey, accessible anytime from the admin console.
- Export for compliance: Generate a CSV of all recovery keys for HIPAA, GDPR, SOC 2, or internal audit requirements.
- Automate protection: Set policies to lock or wipe devices when they leave designated safe zones -- an extra layer beyond BitLocker alone.
- Stay compliant: Meet data protection standards like ISO, HIPAA, and GDPR without added complexity.
Securing your data should not feel like a chore. With Prey's Disk Encryption, your team can focus on what matters most -- knowing that recovery keys are stored, compliant, and retrievable whenever they are needed.
Frequently Asked Questions
How do I enter a BitLocker recovery key?
When prompted, type the 48-digit key exactly as it appears. You must enter it on the same device where the drive was encrypted -- it will not work on a different machine. If you have the key saved as a file or printed copy, type it in manually when the recovery screen appears.
How do I get out of BitLocker recovery mode?
Enter the correct 48-digit recovery key when prompted. Once validated, the device resumes normal operation. If you are stuck in a loop where the recovery screen appears every startup, check for recent BIOS changes or added/removed hardware -- these are common triggers.
Is there a BitLocker recovery key generator?
No. A BitLocker recovery key is a unique 48-digit password generated by Windows when BitLocker is first enabled on a specific device. It cannot be regenerated or retrieved through any third-party tool. Back up the key from the moment BitLocker is activated -- there is no way to recreate it later.
How do I unlock my drive using the BitLocker recovery key?
At the BitLocker recovery screen, enter the 48-digit key exactly as stored. Windows validates the key and unlocks the drive, allowing normal login. You do not unlock the recovery key itself -- you use it to unlock the encrypted drive.
What happens if I lose my BitLocker recovery key?
If the key is lost and not stored anywhere -- Microsoft account, Azure AD, Active Directory, Intune, or Prey -- the data on the encrypted drive is effectively unrecoverable. Microsoft does not store personal recovery keys. As a last resort, resetting the device with Windows recovery media erases all data permanently.
Can IT admins retrieve BitLocker keys remotely?
Yes. IT admins can retrieve keys from Azure AD/Entra ID, Microsoft Intune, Active Directory, or Prey. Admins can also use the Microsoft Graph PowerShell API or run manage-bde -cn [ComputerName] -protectors -get C: against remote machines with an active Windows session.
Where does BitLocker store the recovery key on the device itself?
It does not. By design, BitLocker does not store the recovery key on the encrypted drive -- that would defeat the purpose of encryption. The key is always stored externally: in a Microsoft account, Azure AD, Active Directory, Intune, Prey, on a USB drive, or as a printed copy.
How often does BitLocker ask for the recovery key?
Normally, almost never. BitLocker only prompts for the recovery key when it detects something unexpected during startup -- hardware changes, firmware updates, BIOS modifications, or failed authentication. If you are seeing the recovery screen frequently, investigate recent system changes or contact your IT team.




