Not every device needs the same level of tracking. A CEO's laptop, a warehouse tablet, and a student Chromebook each carry different risk, privacy, and battery constraints. Customizable tracking lets you decide how often Prey checks in.

Customizable Device Tracking setting
More resources
Monitor entire company domains for leaked credentials on the dark web, built for organizations with large teams and multiple email addresses.

Learn how to flag a missing device, gather evidence for recovery, review activity logs, and trace location history.
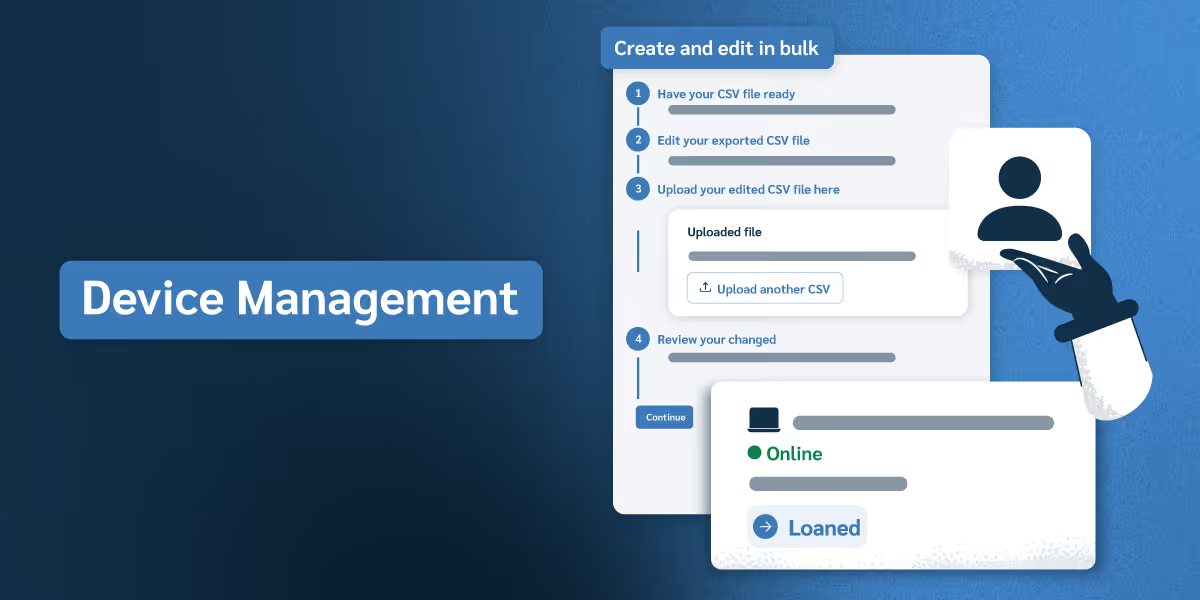
Explore how to organize devices, manage user roles, track asset checkouts, and maintain audit-ready records across your organization.