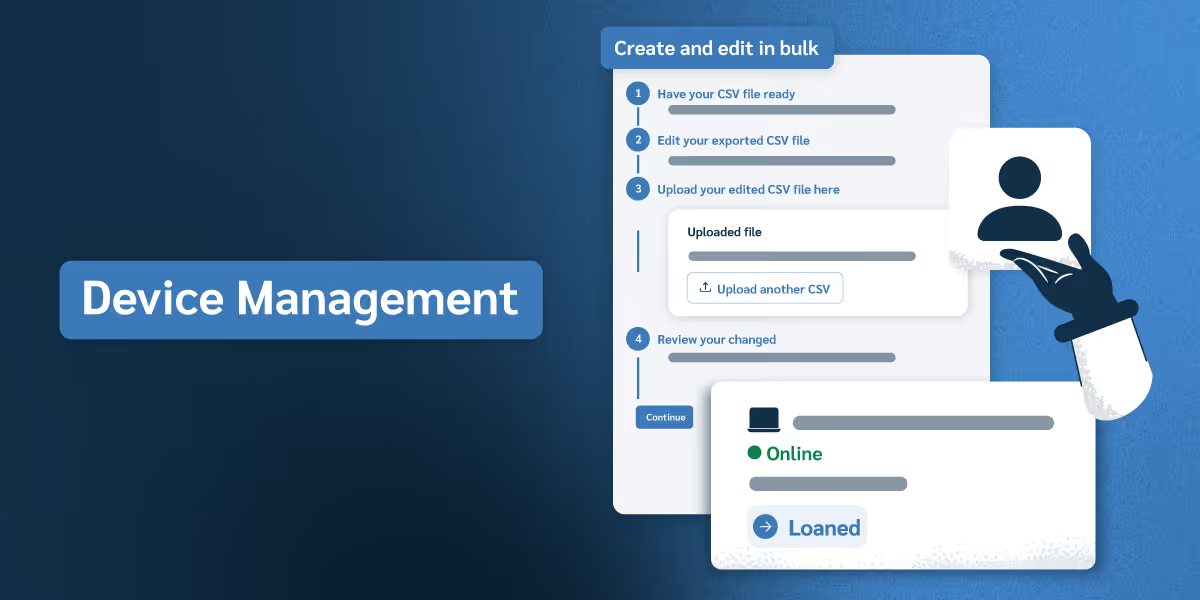
Your devices aren't supposed to leave the hospital, the campus, or the warehouse but how do you know when one does? Location-based security draws virtual boundaries around every approved zone and lets Prey act the instant a device crosses the line. Lock the screen, trigger an alarm, generate a missing report with photos and screenshots, or escalate to remote wipe, all based on rules you set once.
Combine with time-based automations for after-hours enforcement, or inactivity triggers for idle devices. Proactive security that runs on its own, so your IT team isn't the one chasing devices across a map.