See Prey in action
Explore how Prey helps IT teams track, protect, and manage every device.

Recommended
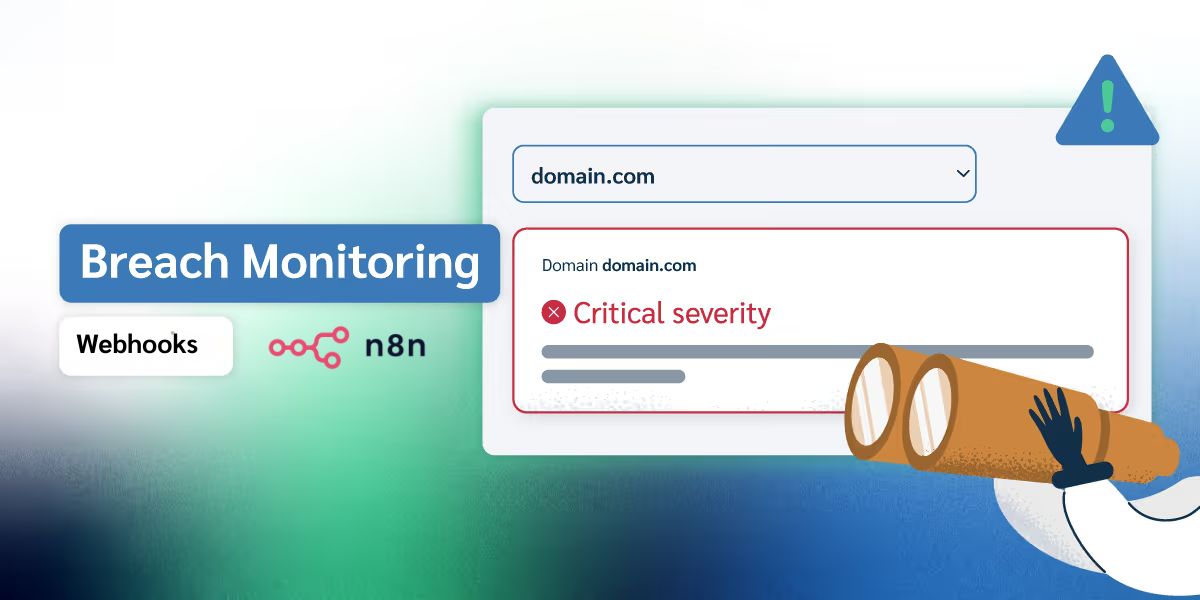
From active status tracking to automated external workflows, see how Prey’s latest updates turn raw leak data into an organized response plan.
See how Prey works
See how Prey pinpoints any device on a map, traces its location history, and alerts you when it crosses a geofence all from one panel.

Learn how to flag a missing device, gather evidence for recovery, review activity logs, and trace location history.
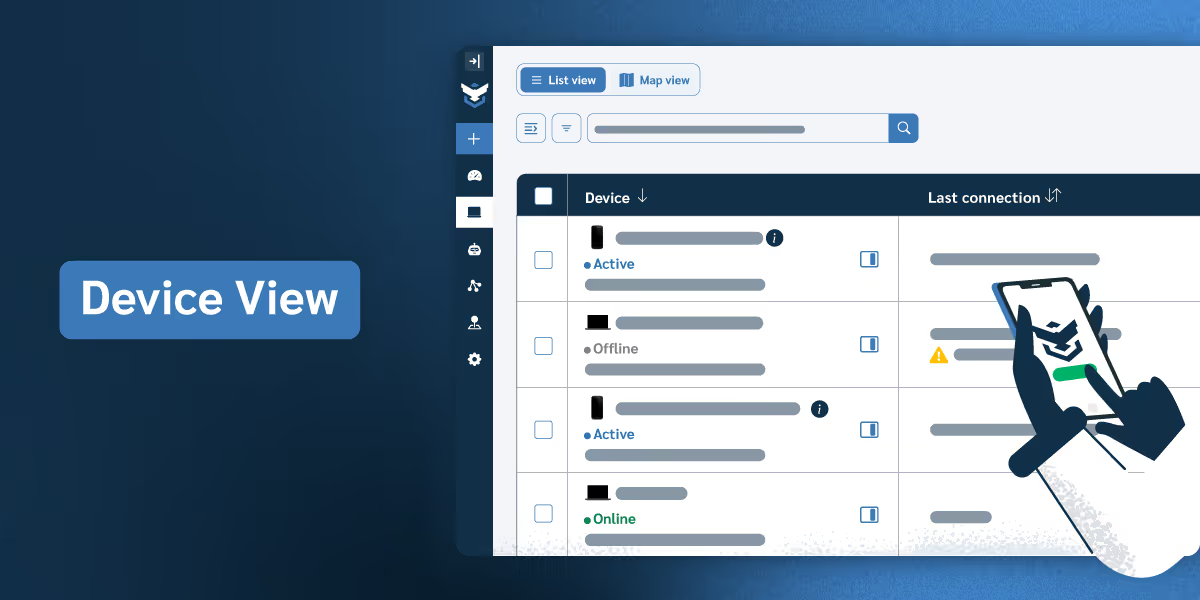
Get to know your panel's main page: the central hub where you monitor connections, status, and details for every device in your fleet.
Did you know Prey's tracking services are always-on? Let's see the data in the panel.
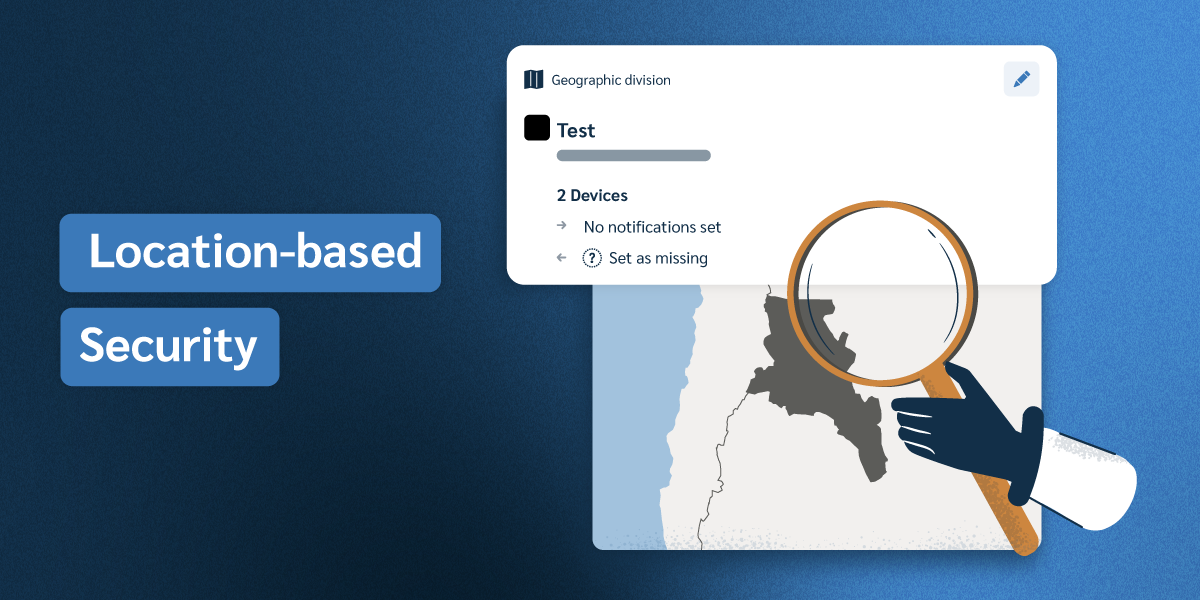
Set geofences around approved zones and let Prey enforce the rules 24/7, lock, alert, or wipe automatically when a device crosses.
Features
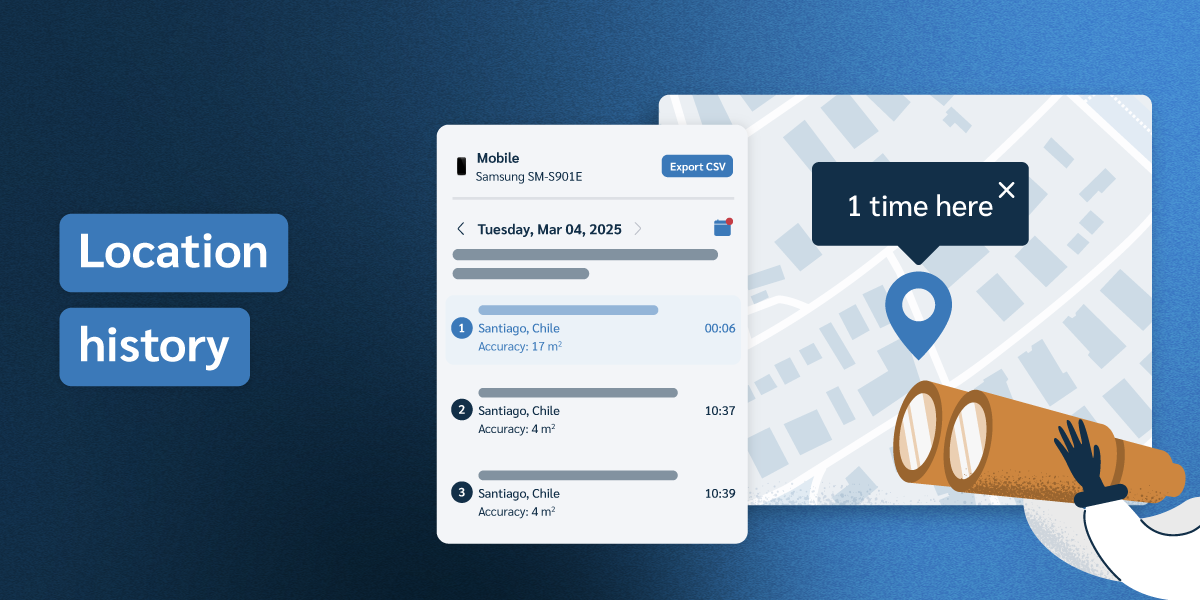
All your fleet's devices store a Location history log for up to a month. Let's review this comprehensive feature
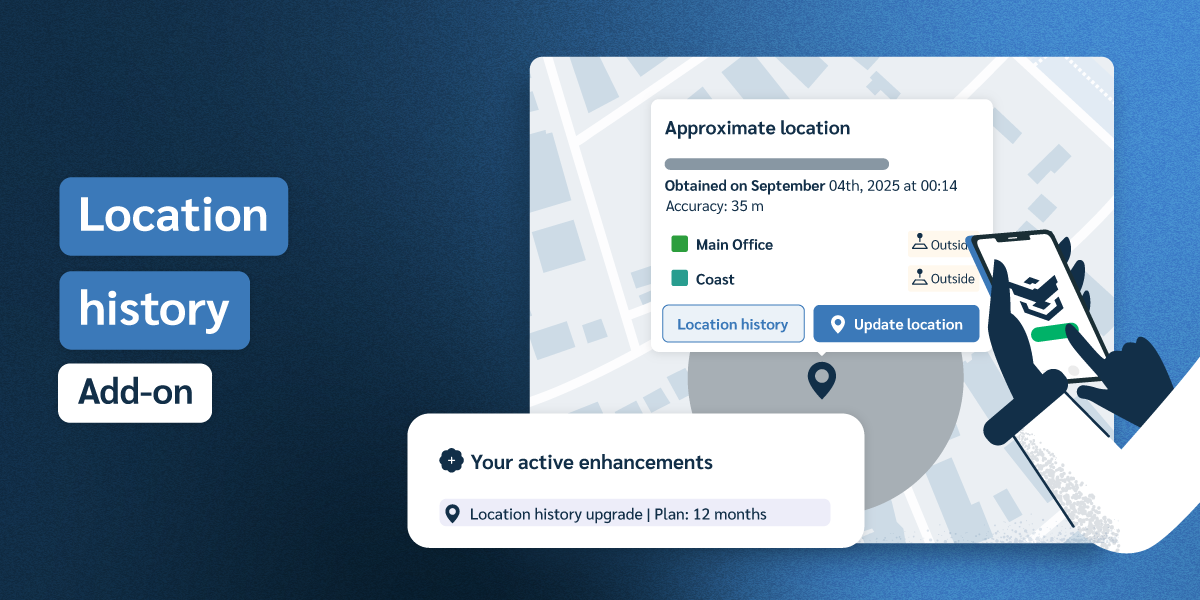
We introduce a new, add-on upgrade to our service: Extended Location history.
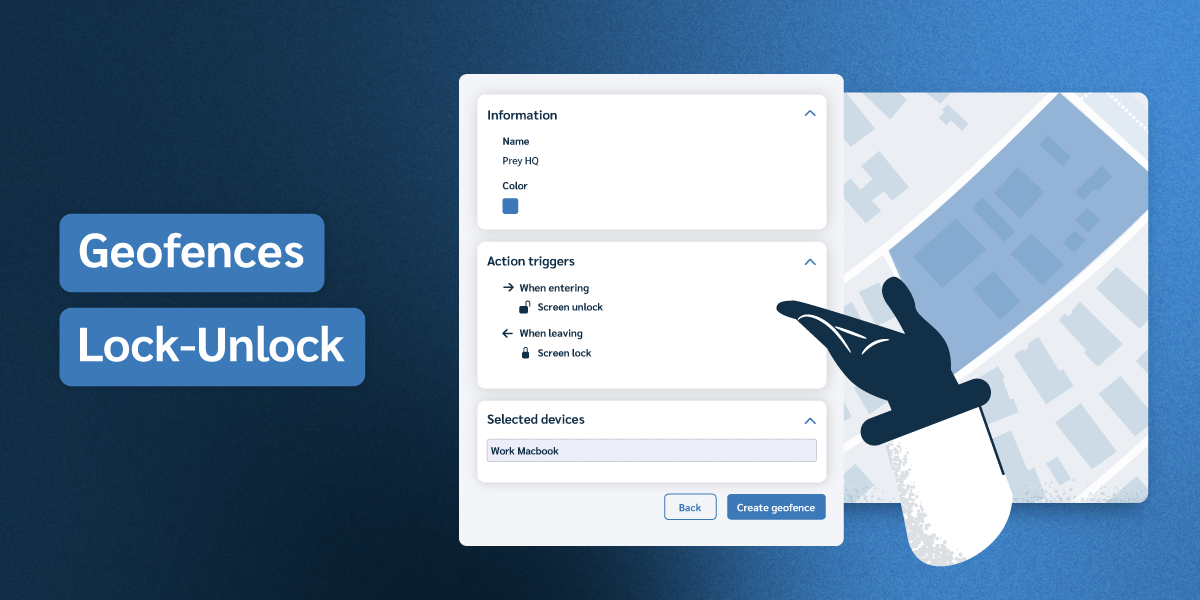
Set geofences around approved zones and let Prey enforce the rules 24/7 — lock, alert, or wipe automatically when a device crosses.
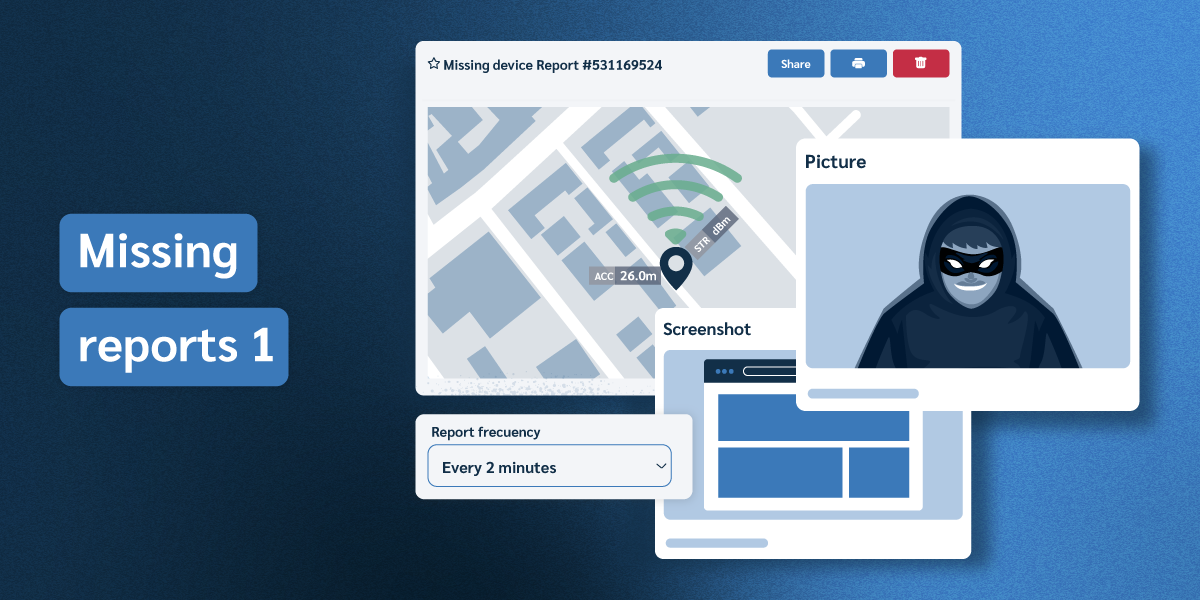
Learn more about mark as missing feature and then review a typical missing report.
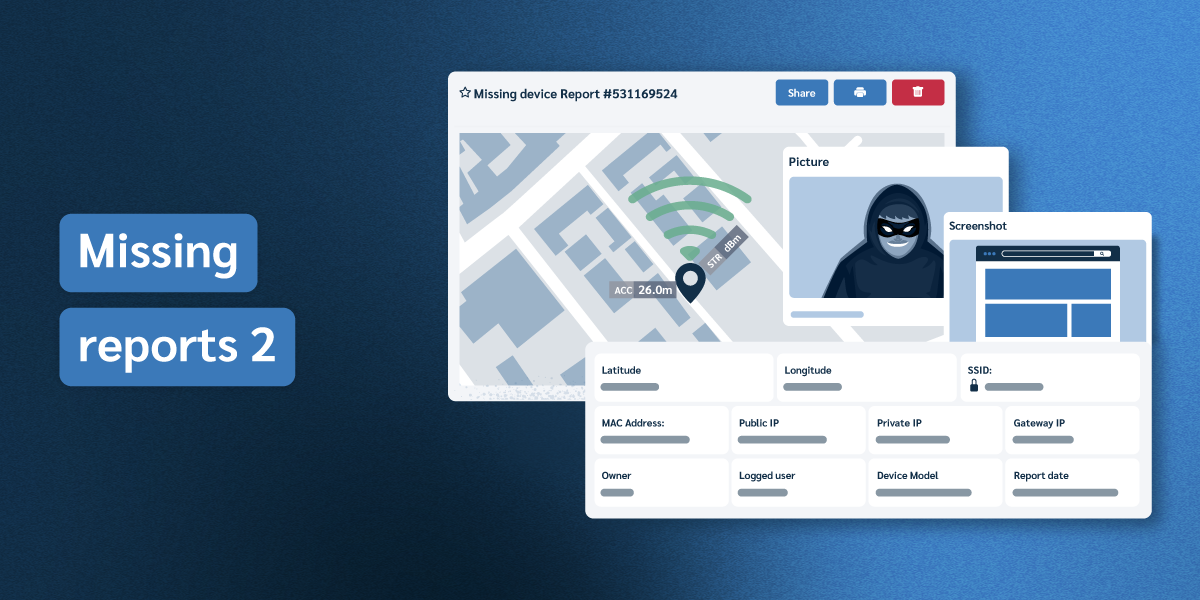
Devices marked as Missing gather automatic informative logs for overall accountability.

Learn how to remotely wipe, encrypt, and retrieve files from a lost or stolen device before sensitive data is exposed.
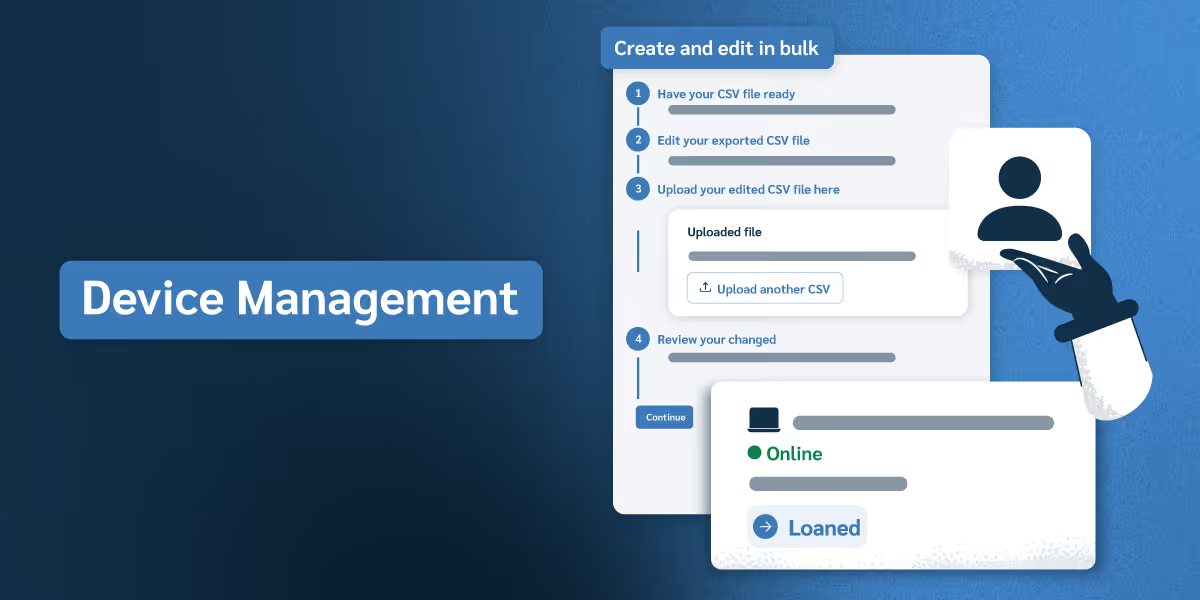
Explore how to organize devices, manage user roles, track asset checkouts, and maintain audit-ready records across your organization.

Prove policy enforcement, not just document it. Automate security rules
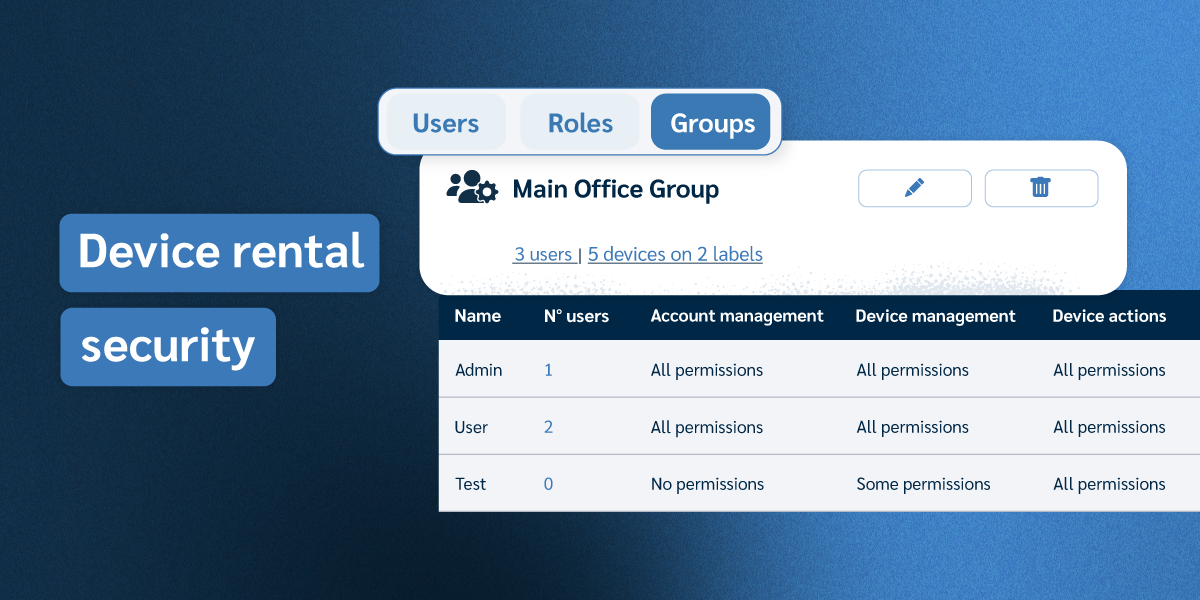
Track, protect, and recover rental fleet devices. Enforce contracts, lock unreturned units, and wipe data on leased endpoints.
Features
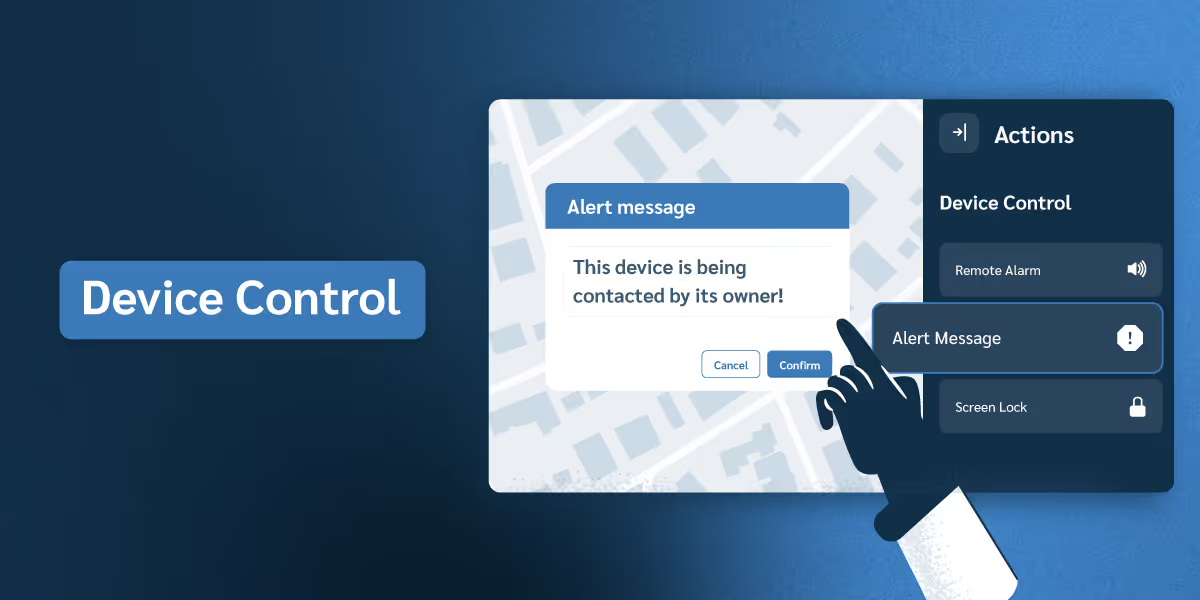
See how to take control of any device remotely and set up automated security responses that trigger without manual intervention.

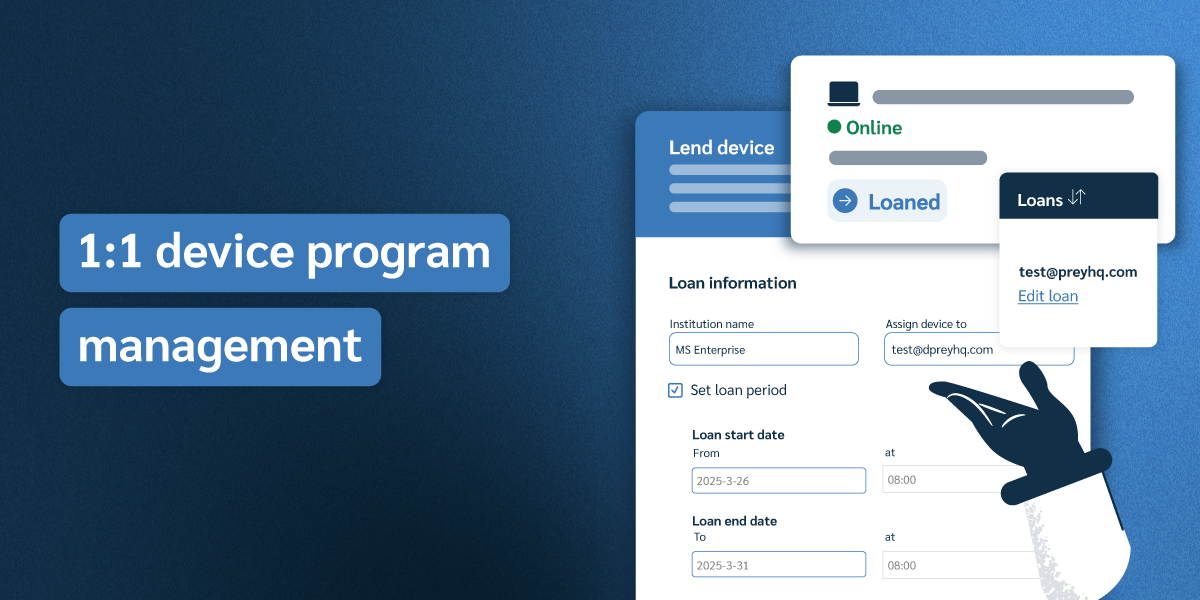
Manage 1:1 device programs without the spreadsheet chaos. Track assignments, flag overdue returns, and recover devices automatically.
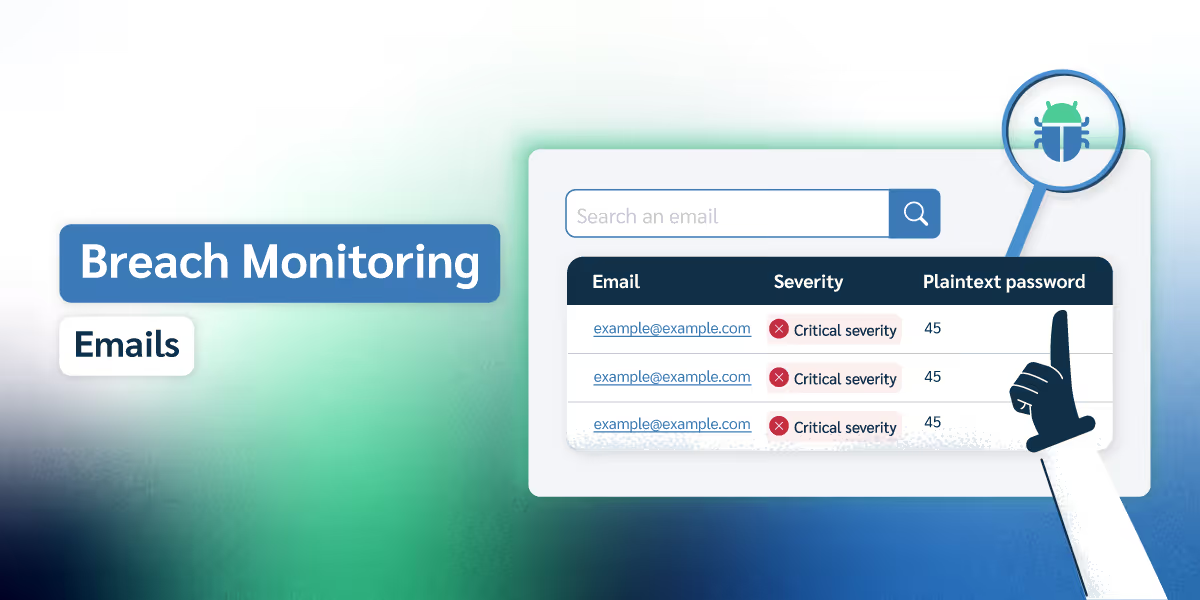
Track individual email addresses for dark web exposure — ideal for monitoring C-level executives, key clients, or high-risk accounts.
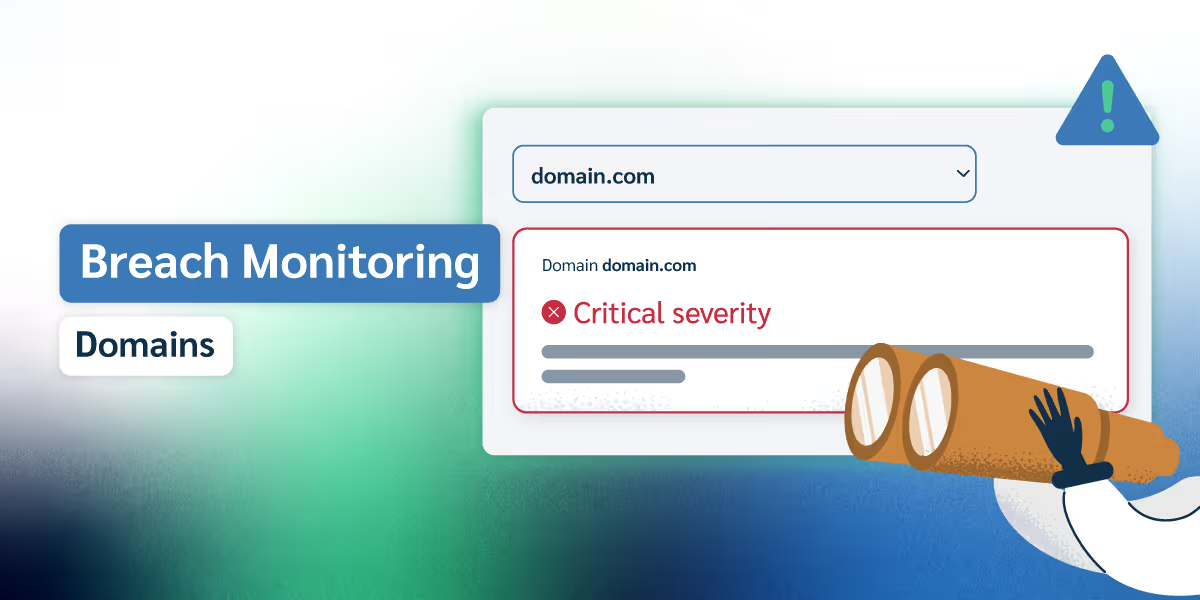
Monitor entire company domains for leaked credentials on the dark web, built for organizations with large teams and multiple email addresses.
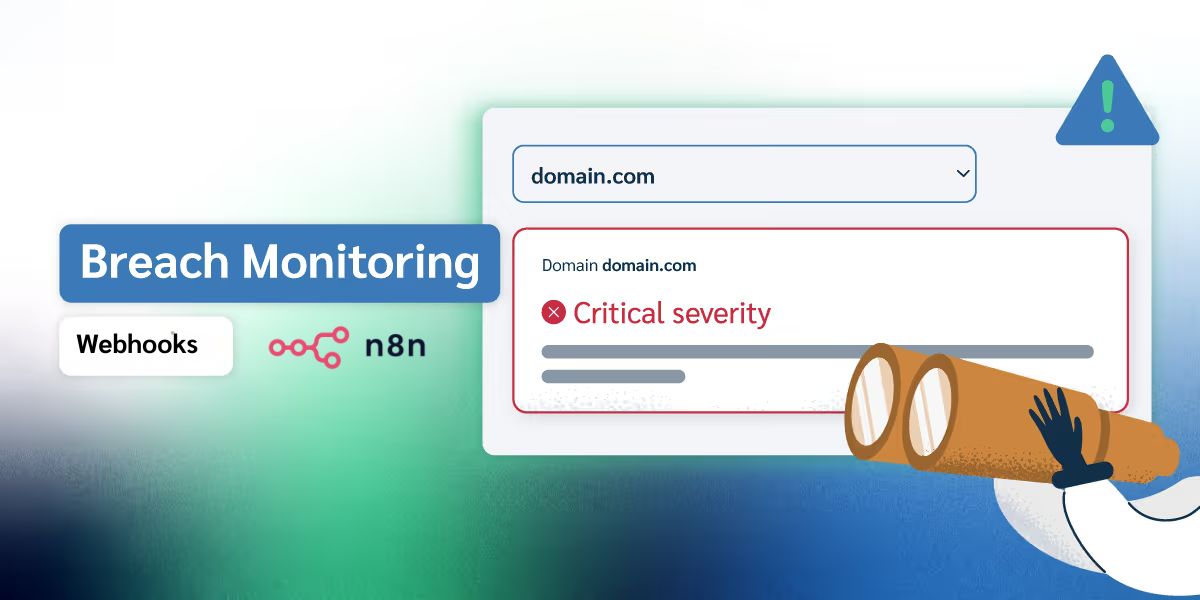
From active status tracking to automated external workflows, see how Prey’s latest updates turn raw leak data into an organized response plan.

